With the increase in Global security threats Information Risk Management (IRM) is the call of the hour.
Merino is providing to its valued customers - complete Information Security Lifecycle Management (ISLM) based on leading edge technologies, ML, Advanced AI and strategic partnerships globally.
With 150+ years of Team Experience in Cyber Security our services are uniquely positioned to address every aspect of it - from your edge to the core & beyond boundaries.
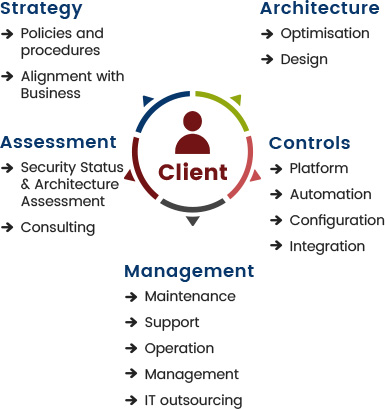

Looking forward to be your preferred partner for the complete IS Life Cycle Management and/or start from any point…
| Access Management | Asset / Config Management | Change Management |
| SIEM / SOAR | Identity Management | Vulnerability / Patch Management |
| CASB | Data Encryption | DB Activity Monitoring | Document Exchange |
| MDM | FIM | Security Analytics | WAF |
| IDAM | SSO | PAM | DAM |
| Antivirus / HIPS | Configuration Management | EDR |
| Host DLP | Patch Management | Vulnerability Management |
| AAA | MFA | NAC | PAM |
| Cyber Deception | DDOS Protection | DNS | Email Gateway |
| Firewall | IPS | Network Antivirus | Network DLP |
| Network Sandboxing | SSli | VPN | Web Gateway |
| Wired | Wireless |
| Feeds | Platform | Analysis |

